I first got into Unix in 1987. SunOS 3 on the Oxford “mclab” network (who else remembers “NFS server pampa not responding, still trying”?). At the same time I had access to the “High Level Hardware Orion” machines, in the Clarendon Nuclear Physics lab as a member of Oxford Microsoc.
I had no idea what I was doing. But I learned pretty quickly!
My first job was as a SA for Papachristidis Limited; a Greek shipping based out of London. It was a small office so I ended up doing almost everything (coding, networking, SA, fax machine, telephones, even the door entry security system). It was a good place to learn and hone my skills.
At this point I started with Linux (0.11 kernel) and even got interviewed by Linux Journal.
Around the same time I took over the running of Spuddy (link to old old old spuddy website), which provided free email and usenet in the UK. Basically a Sun 2 with a Magma serial port extender and a handful of modems. A British Telecom engineer once claimed I had more phone lines in my spare bedroom than some companies! Spuddy even got written up in the national computer press and was compared favourably to commercial providers.
My next job was at VNU Business Publications in London, working in a startup division called MatriX Publishing Network. (I remember one of the staff members claiming “We got Spuddy!” when I accepted the contract). I did SA, networking, web development, I even wrote a few magazine articles. The division got shut down (we were making a profit, but not in the core business areas) and I moved into the central IT team where I began my path of automation and centralisation; rolled out Big Brother, created a paging sytem, backups… Eventually I had the Unix servers under control so they made me learn Oracle DBA… then Windows NT4 admin… and then Lotus Notes (at which point I ran away).
In 1999 I started to work for JPMorgan (now JPMorganChase). I’ve been in various roles in that company. Most recently I did cloud security engineering. And in 2016 I started with First Data.
DISCLAIMER: Nothing I write can be considered official policy of any company I have worked for. It’s just my opinion. And, hey, I have opinions! In the long long distant past of usenet I had a signature:
The truth is the truth, and opinion just opinion. But what is what?
My employer pays to ignore my opinions; you get to do it for free.
I hope my employers now listen to my opinions, but you can still ignore them!
But my life with computers started before then. In 1981 I started to play with the school’s Commodore PETs. I taught myself 6502 assembler from a book and hand assembled some simple stuff. Like lots of kids I typed in listings from magazines and then debugged the typos.
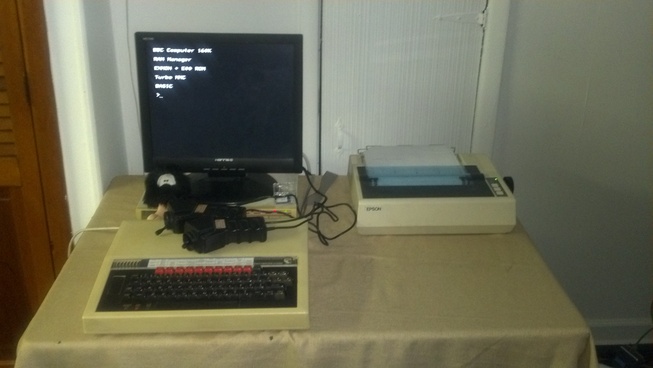
For Christmas 1983 I got my own computer; a BBC Micro. I still have it!
So 1984 was when I started to hit my stride. And that’s when I first learned that people will break things; without trying! My brother was a great help, here. I recall writing him a simple “football score emulator” (each team had a random weighting and the program would create score cards, similar to that shown on TV every Saturday). I presented a menu and expected people to enter “1-22”. My brother typed in the team name. Whuh? Naturally the program crashed (out of range error).
And this is where I started my “security” journey. All the way back over 30 years ago. I taught myself defensive coding; sanitise and validation of input. As time went on those techiques grew into general purpose rules (e.g. “don’t trust the client”).
When the web became popular and people stuck validation routines into their javascript but didn’t implement them at the backend then I laughed; and demonstrated their folly.
But I’ve never been a hacker; not really. I’m not a “security researcher”. I’m not a trained security individual (no CISSP, here!). I don’t play “defense” or “offense” in the infosec world, although I have a tendancy towards defense.
What I am, though, is a security aware person. I have over 30 years of experience and can apply it to new situations. Build “secure from the start” solutions. Take a newly found bug and evaluate it. This puts me somewhere between “risk evaluation” and “security”. It’s a role I don’t see many people filling!
Which leads, inevitably, to my CV (or resume, in American) (PDF).
Note that this blog is inherently an “enterprise” view of the world. An organisation with controls requirements, potentially regulators and auditors.
But some of the concerns also affect everyone; do you want to run code that is hackable? That causes an RCE (Remote Code Execution) and so people can “pivot” and attack other servers? Even education research environments should care about this.
So if you’re interested in a non-sensational (I hope!) viewpoint on modern internet security as it pertains to the enterprise, maybe this blog will be a good place to look.
I can’t promise frequent updates; I can’t promise 100% accurate evaluations. But it may still be interesting.
If you need to contact me for any reason and leaving a comment on a blog post entry isn’t what you’re looking for then here’s my business card!
And who are you reading? Well, this is me… or it was in 2016, anyway!

