3 years ago I replaced OpenWRT with a home grown router.
It’s worked pretty well, but I wanted to take advantage of improvements in networking (5Ghz!) and also improve coverage. This kinda became important due to COVID lockdown and Work From Home. My library, where I was working from, had very weak network signal. I needed to do better.
So I decided to look at turning off in the inbuilt WiFi and use an external WAP (Wireless Access Point, or just AP). However I wanted to keep using the Multi-SSID setup I had, to allow for LAN and Guestnet access (and since that post I also added an IoT network, although I’m not sure I’m gonna keep it).
The obvious way of doing this, on Linux, is to use 802.1q VLANs and then
have the AP map the SSID to the VLAN. In that way traffic from the LAN
network would still appear on the br-lan bridge on the router and
everything would work the same way.
I might write another post, later, explaining 802.1q but for now you can imagine it’s a way of having multiple virtual LANs all running over the same cable. Each virtual LAN gets a number between 1 and 4095, and the switches can decide what ports get to see the traffic. This allows you to create a backbone network, but still only pass relevant traffic to different network segements. What I’m doing, in this post, is defining a network backbone of 3 VLANS, but endpoints (eg my desktop, or a phone on the guest wifi network) acts is if it was on a dedicated network.
Switches
Now this requires switching equipment to also be able to understand 802.1q tagging and be able to make some ports dedicated to various networks, and make other ports “trunk” networks, able to pass traffic for multiple networks.
I picked the TP-Link SG116E switch for this. It’s a 16 port Gigabit switch and can handle 802.1q VLANs. I got two of these; one for my basement (where the existing switch is) and one to replace the living room switch.
Now, arbitrarily, I chose VLAN 10 to be my main LAN, VLAN 11 to be for Guestnet and VLAN 12 to be for IoT.
Router config
On the Linux router this is done by configuring “sub-interfaces”
% cat ifcfg-enp3s0.10
DEVICE=enp3s0.10
TYPE=Ethernet
ONBOOT=yes
BRIDGE="br-lan"
NM_CONTROLLED="no"
VLAN=yes
This simple configuration will add the “enp3s0” sub-interface 10 to the
br-lan and any traffic sent out of it will have an 802.1q tag value of
10.
Interfaces “.11” and “.12” are similarly configured.
So now the bridging table would look something like
bridge name bridge id STP enabled interfaces
br-guest 8000.000db9439cce no enp3s0.11
br-iot 8000.000db9439cce no enp3s0.12
br-lan 8000.000db9439ccc no enp3s0.10
br-wan 8000.000db9439ccd no enp2s0
(I’ve hidden the hostapd entries for WiFi since I’m gonna turn that
off in a little while, and it’ll just confuse things)
The wisdom of building these bridges, earlier, is now paying dividends. I can add new networking constructs to the bridges and it “just works”.
Back to the switch
I now need to configure the switch to understand this. I plug the router port 3 (“enp3s0”) to the switch port 1. And I configured the switch so that port 1 is tagged VLANs 10, 11, 12 and every other port is untagged VLAN 10.
At this point we haven’t gained anything; everything on the wired network is still all LAN traffic. But we’ve got VLAN tagging between the router and the switch. So we’ve now got potential.
Next step is to do similar for the switch in the living room, behind the TV. I similarly configure that switch so port 1 is tagged 10,11,12 and the rest are untagged 10. I can now configure basement port 7 (don’t ask!) to be tagged VLANs as well.
So now all the VLANs exist in both the main switches, even though all the client machines are on VLAN10 (LAN) only.
Access Points.
I’m now ready to start putting APs on the network.
I looked at mesh networks, but most of the kit wasn’t able to do multi-SSID to VLAN mappings. They’re great at coverage, but if I can’t do the networking constructs I want then they’re useless to me. It’s possible the Ubiquiti products can do this, but they’re very expensive. If you want prosumer, go that path. I decided to go down the DIY path.
Which meant delving back into the OpenWRT world. Some research (and a sale at Amazon) lead to buying 3 TP-Link Archer A7 routers. These can very easily be flashed with OpenWRT. They can then be configured to act as APs and not routers. It took a few trial and errors to understand what the document and examples meant when it came to multiple VLANs and multiple SSIDs, but eventually I got it.
I avoided re-using constructs the base software uses (eg the WAN port, or the network names WAN and LAN, and VLANs 1 and 2). So I’m just going to use the 4 LAN ports and build three networks Main, Guest, IoT
Only the Main network needs to have an address ‘cos that’s how you’ll talk to the AP later.
Defining AP VLAN ports
OpenWRT being Linux, you have similar sub-interface addressing for VLANS.
We also need to tell the switch what ports are on what networks.
BE VERY CAREFUL HERE. If you get the setup wrong you can lose network connectivity to your AP and then have to fight to get it back. I’m going to describe the target state but not how to get there in each step. It’s worth leaving at least one port on LAN and keeping that configured so the original 192.168.1.1 address is still visible on that port… just in case :-)
But at the end of the day, in the main main network/switch menu you will end up with a config similar to:
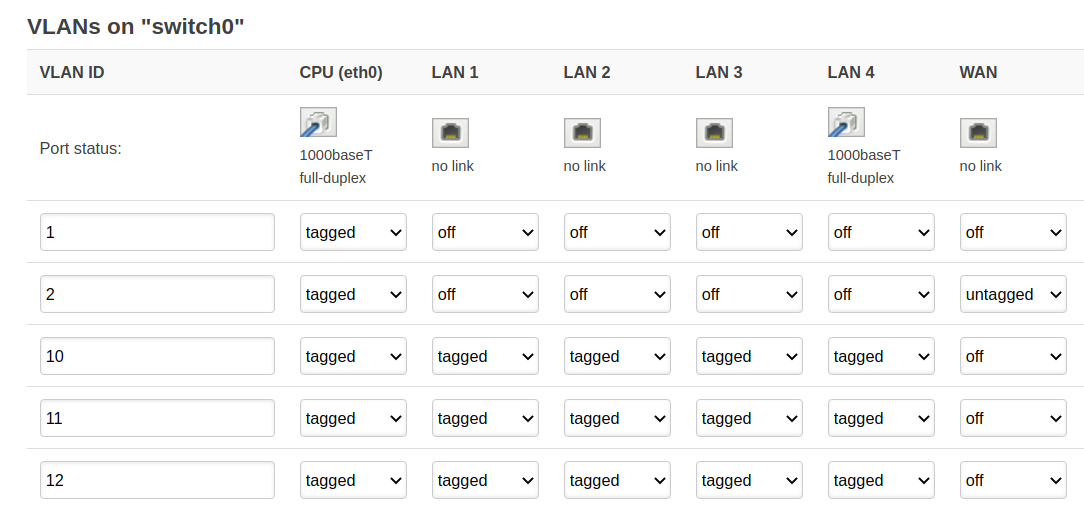
This tells the AP to configure all 4 LAN ports as tagged for 10, 11, 12. In this case I have port 4 plugged into the main switch, which is also set for tagged VLANS. VLAN1 was the original VLAN used by the software to manage the LAN, and VLAN2 is for the WAN. It’s possible (but I haven’t tested) to remove VLAN2 from the WAN port and add that to 10,11,12.
The equivalent in /etc/config/switch is
config switch
option name 'switch0'
option reset '1'
option enable_vlan '1'
config switch_vlan
option device 'switch0'
option vlan '1'
option vid '1'
option ports '0t'
config switch_vlan
option device 'switch0'
option vlan '2'
option vid '2'
option ports '0t 1'
config switch_vlan
option device 'switch0'
option vlan '3'
option vid '10'
option ports '0t 2t 3t 4t 5t'
config switch_vlan
option device 'switch0'
option vlan '4'
option vid '11'
option ports '0t 2t 3t 4t 5t'
config switch_vlan
option device 'switch0'
option vlan '5'
option vid '12'
option ports '0t 2t 3t 4t 5t'
The numbers “0 1 2 3 4 5” on the option ports line refer to ports
seen in the diagram, but the ordering can change on different equipment.
On the A7, 0 is CPU, 1 is WAN, 2->5 are the LAN ports. This is common,
but not always true! That’s why it’s worth doing that bit in the GUI,
to let it pick the port numbers.
We can then define the 3 bridges (“interfaces” in OpenWRT speak) and associate them with the VLANs (also in the same config file).
config interface 'Main'
option ifname 'eth0.10'
option type 'bridge'
option delegate '0'
option proto 'static'
option netmask '255.255.255.0'
option ipaddr '10.0.0.249'
config interface 'Guest'
option proto 'none'
option type 'bridge'
option delegate '0'
option ifname 'eth0'
config interface 'Iot'
option ifname 'eth0.12'
option proto 'none'
option type 'bridge'
option delegate '0'
So now we have the AP configured on the ethernet site and can be plugged into a trunk port on the switch.
Defining AP WiFi
Onto WiFi!
From the Network/Wireless menu you can simply add new networks to each Radio (2.4Ghz and 5GHz). The setup would look similar to:
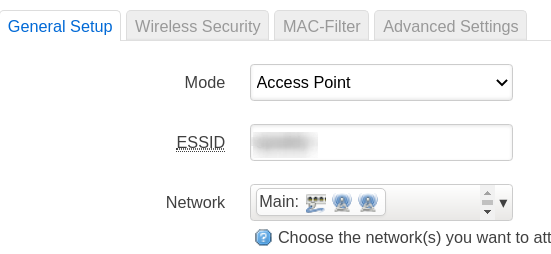
Remember to set a WPA2 key on the security TAB. For me that meant adding entries for the Lan/Guest/IoT networks and selecting the relevant interface. It’s boring, but works.
At the end, in /etc/config/wireless you’ll see entries similar to:
config wifi-iface 'wifinet1'
option device 'radio1'
option mode 'ap'
option network 'Main'
option encryption 'psk2'
option key 'MYPASSWORD'
option ssid 'MYSSID'
You should see entries for each of the SSIDs and for both radio1 and
radio0.
You can see the OpenWRT eventually built network structures very similar to what my original router config had:
# brctl show
bridge name bridge id STP enabled interfaces
br-Guest 7fff.74da88a9a43b no eth0.11
wlan1-1
wlan0-1
br-Main 7fff.74da88a9a43b no eth0.10
wlan1
wlan0
br-Iot 7fff.74da88a9a43b no eth0.12
wlan1-2
wlan0-2
br-lan 7fff.74da88a9a43b no eth0.1
After all of this hard work, we’re kinda back where we started.
We have an AP presenting the same 3 wireless networks as before and they’re on the same router bridges as before, and so the same firewall and routing rules work.
Replication
So why go to all this hard work?
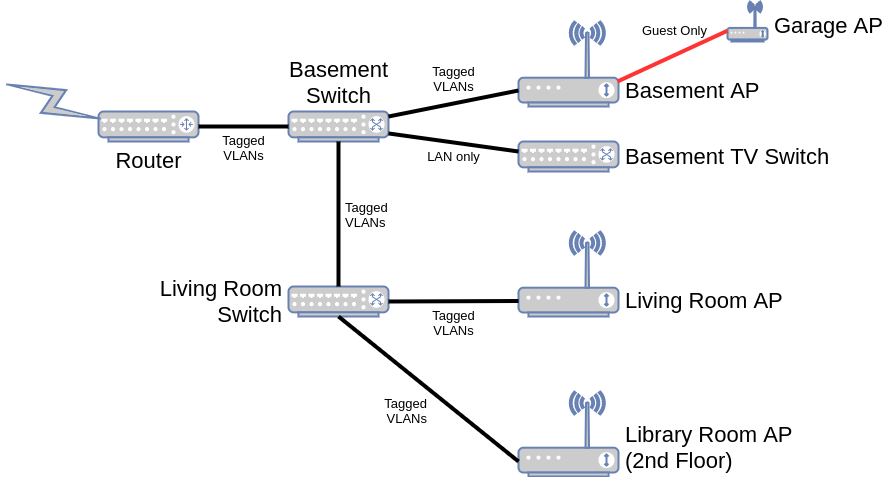
Well, now we can replicate this. I can put one of these A7s behind the TV in my living room (pretty much central to the house). I can put one in the laundry area of the basement at the back of my house. And I can put a third one in my library, with an ethernet cable running to the living room TV switch. I chose different frequencies for each one, so they don’t fight for airwave bandwidth!
Which is what I did. And it works… adequately. OpenWRT doesn’t currently have “beam steering” available, so when I walk from one room to another then my phone might decide to fall back to the slower 2.4Ghz, rather than stay on 5Ghz. And, oddly, machines don’t always connect to the closest AP (why would a smart plug in the laundry, literally 4ft away from the AP, decide to connect to the one in the library, 2 floors away?)
But despite this, it works well. I have strong signal everywhere.
Garage
With one caveat. My garage. When the metal door is closed it seems to reduce the signal strength just enough to cause my smart dumb opener to lose network signal.
So for that I used a TP-Link AC750 Powerline adapter. I found a plug in the basement (conveniently close to the basement A7) that was on the same circuit as the garage electrics. So I was able to use one port of the A7 to be untagged Guestnet and plugged the Powerline adapter into that. It works.
The power of 802.1q aware switches (which my core switches and the A7s are) is that they can extend and expose any of the networks, so I could even expose a hardwired Guestnet port from any of these switches.
Port Summary
Basement:
VLAN VLAN Name Member Ports Tagged Ports Untagged Ports
1 Default_VLAN
10 lan 1-16 1-3,7 4-6,8-16
11 guest 1-3,7 1-3,7
12 iot 1-3,7 1-3,7
Port 1 goes to the router; 2 is my “test” port and is currently unused, 3 connects to the basement A7 and 7 connects to the Living Room switch. All other ports are on the main LAN
Living Room:
VLAN VLAN Name Member Ports Tagged Ports Untagged Ports
1 Default_VLAN
10 lan 1-16 1-2,12 3-11,13-16
11 guest 1-2,12 1-2,12
12 iot 1-2,12 1-2,12
1 goes to the basement switch, 2 goes to the living room A7, 12 goes to the library A7. All other ports are on the main LAN.
Finally
And just for completeness, I have a dumb Gigabit switch in the basement on the far side from the router and core switch. This is used for my “exercise entertainment” center; I have an old old TV, an old Mac Mini, a TiVo Mini, a Pioneer Amp and a FireTV stick there. These need networks, so I ran a cable around the room and put a dumb switch (my original gigabit switch before I went VLAN aware) there.
So my final network looks like: